Secure.
Simplify.
Scale.
AI+Cybersecurity
Built for Normal People
We help regular businesses integrate cybersecurity
into their everyday operations through the power of AI

Securing your entire digital operations has never been easier
We are building cybersecurity for businesses of all shapes and sizes, from the global brand in Johannesburg to the corner shop in Agege!

Secure
Delivering enterprise cybersecurity in natural human language

Simplify
Deploying AI agents to simplify critical business operations

Scale
Focus on scaling while AI agents handle the security
Features
Cybersecurity should be simple and affordable
A cybersecurity team on your mobile device
With agentic cybersecurity, you have a full SOC team that you control from a simple dialogue box on any device.
Speak human language, get superhuman results
Eliminate human error. Communicate with your team of robots in human language and have them operate with superhuman efficiency.
Meet local and global compliance requirements
From NDPA in Nigeria to POPIA South Africa, your agentic cybersecurity team will help you meet full compliance across multiple industries.
How it works
Simple steps, powerful protection: see how Agentic Cybersecurity keeps your business safe.

Onboard Your AI Cyber Team!
Ditch filling in rigid forms! Simply explain your operations in natural language—what your company does, the systems you rely on, the type of data you handle, and any industry standards you follow. Provide helpful documents and links. The agents study this information to build an understanding of your environment, so that every security measure applied later is tailored to your specific needs.
You instruct, they secure!
Everything is done in natural language. Simply say, “Ensure only staff in Nigeria can log in,” or “Protect all customer records under NDPA compliance.” The AI agents translate these instructions into concrete security actions such as configuring defenses, tightening access controls, or applying safeguards automatically. Your role is to speak; their role is to secure.
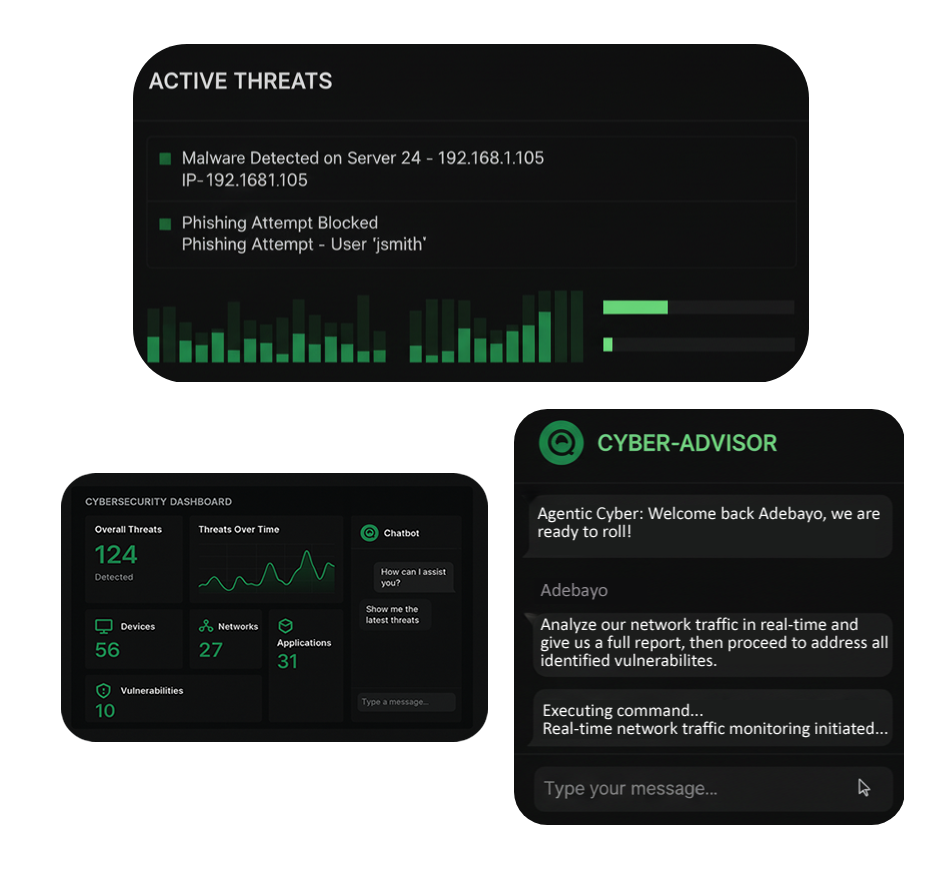

Real-time monitoring and protection
You can instruct the agents activate continuous monitoring to protect your systems in real time. This means watching for unusual activity, scanning for vulnerabilities, and tracking attempted intrusions as they happen. The agents respond in real-time, blocking suspicious access, isolating risky files, and alerting you to threats as they unfold. This step ensures your business is not just configured securely, but actively defended around the clock.
Backed by the Tony Elumelu Entreprenuership Program
Other great minds believe in what we're building
AI Cybersecurity for the African Market...


